TL;DR
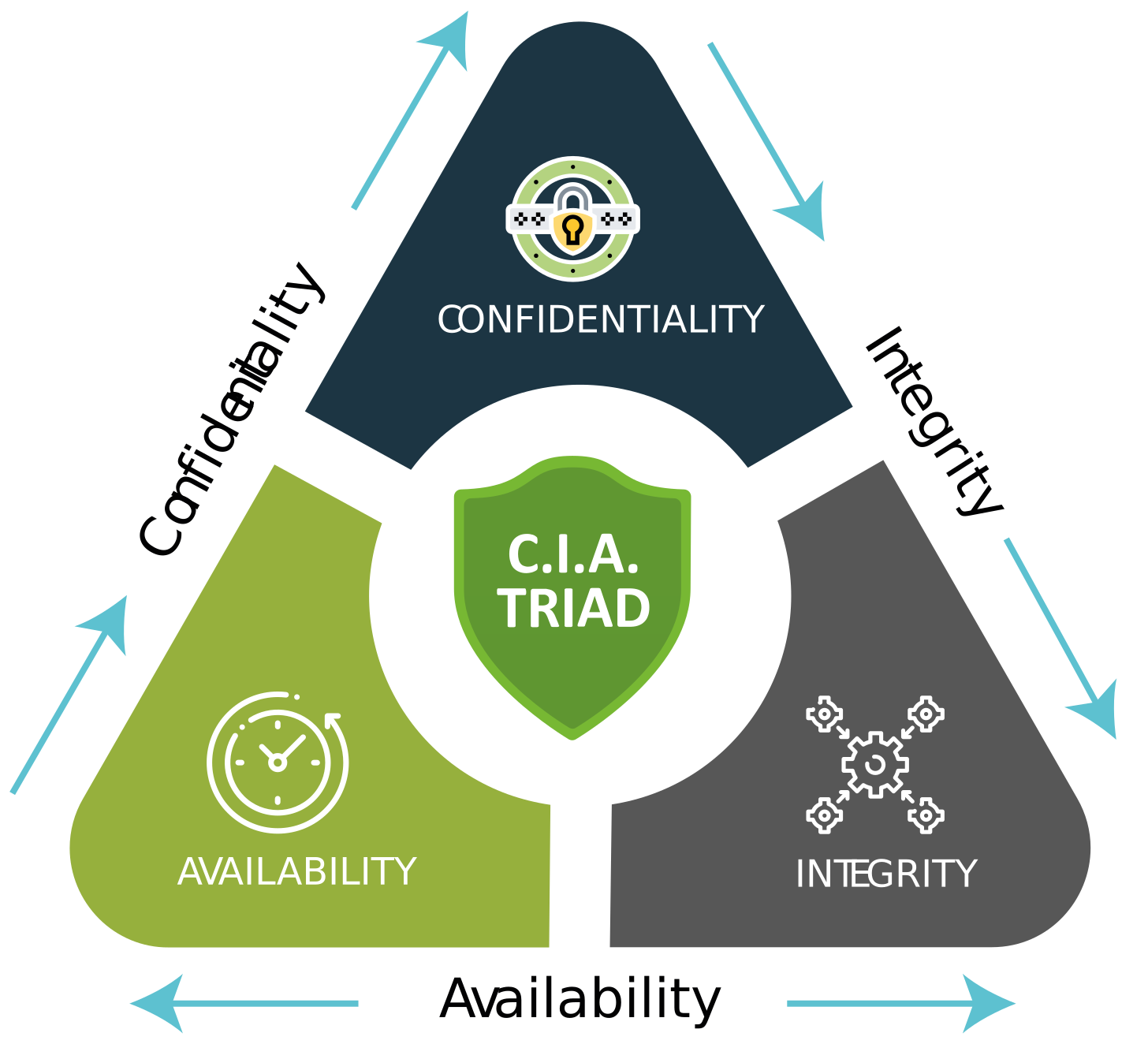
Information classification is a corner stone of cyber security. The famous security triad of Confidentiality, Integrity and Availability (CIA)
The idea is that you rate the information stored, processed and transmitted by a system or collection of Systems Under Change (SUC) and align your cyber security controls to them
In theory this provides the best Return on Security Investment (ROSI) as the most complex and expensive controls protect the most valuable information and features and vise versa
In reality, my argument is that only storage encryption, data loss prevention, penetration testing and supply chain security should change based on CIA
For the majority of your cyber security controls, do a threat model and in general apply to all systems
Introduction
I’m making an assumption that most of you reading this post work in cyber security or technology so are familiar with the following triad:
Thee idea is that for every project or change you analyse and rate CIA e.g.,
Confidentiality - public, internal, confidential. What is the business impact if this information gets exposed to the public or the wrong group of internal or service provider users
Integrity - low, high. What is the business impact if the accuracy of this information gets tampered with by malicious threat actors. E.g., could be high for a regulatory or financial report or straight through payments system.
Availability - 4 hours, 24 hours, 1 week. What is the Maximum Acceptable Outage (MAO) if the system availability is disrupted by threat actors? What is the Recovery Time Objective (RTO) and Recovery Point Objective (RPO).
The standard thesis in cyber security is that your cyber security controls should align to the CIA ratings. The higher the CIA ratings the more numerous and the more stringent security controls should be implemented.
What security controls change with CIA?
Authentication and Authorization - No change
You want to integrate your systems with your Identity Provider (IDP) which will provide password complexity, account lockout, multi-factor authentication and conditional access. This doesn’t change for low CIA systems vs high.
Identity lifecycle and governance - No change
Users and machines need a way to request access, for that access to be approved, segregation of duties checked, access to be automatically be provisioned. Access should adjust for joiner, mover leavers and be regularly reviewed. No change for CIA.
Privileged access - No change
If you have session proxy and session recording capabilities, ability to manage generic and shared accounts including check-in/check-out, just in time access, automated credential revocation you want these to apply to all your systems.
Storage encryption - CHANGE
If you have sensitive data you will want to encrypt this, public or internal data may not need this. However often you will have database tables or storage systems that have a mix and encryption is cheap on both cost and performance to apply, therefore encrypting everything might just be easier.
Transit encryption - No change
Technically if you have public data for example maybe you don’t need to encrypt in transit. But technologies like TLS are just so easy to implement and cheap on both cost and performance to apply just encrypt all flows.
Secure data deletion - No change
Ensure all data you want deleted cannot be recovered.
Data Loss Prevention - CHANGE
You only want to search for data that is sensitive in systems where it should not be and for unauthorized flows
Key lifecycle and secrets management - No change
You want secure generation, transmission, revocation and rotation of all your secrets.
WORM backups - No change
You want all your backups protected against ransomware by making them Write Once Read Many (WORM)
Security Monitoring - No change
You want to monitor all your systems from a cyber perspective driven by usecases
Threat Intelligence - No change
You want to apply threat intelligence to all your security controls and security monitoring.
Network security filtering - No change
You want to reduce the network attack surface for all your systems. You may chose to isolate your high CIA systems but a Zero Trust methodology means really you should do this for all your systems.
Web application FW / Application and Network DOS/DDOS / Bot Protection / API protection - No change
All your inbound flows from the Internet should be protected by a WAF and Application layer and Network DDOS, API protection and bot protection.
Outbound Internet access - No change
All your system outbound Internet access should be filtered by a proxy.
CNAPP - No change
You want to monitor the cloud security posture of all the clouds where your systems run
Network intrusion detection - No change
Your whole network should have coverage by Network intrusion detection / prevention
Secure configuration - No change
All your compute should have a secure configuration with monitoring for drift.
Compute anti-malware - No change
All your compute should have anti-malware
Compute allowlist - No change
All your compute should have allowlisting for binaries that are in the approved image at minimum
Static Application Security Testing (SAST) - No change
All your custom code should be scanned by SAST
Software Composition Analysis (SCA) - No change
All your dependence, libraries and built artifacts should be scanned by SCA
Dynamic Application Security Testing (DAST) - No change
All your Internet accessible systems at least should be scanned by DAST
Infrastructure as Code scanning (IaC) - No change
All your Infrastructure as Code should have security scanning
Penetration testing / Red / Purple team / Attack and Breach Simulation - CHANGE
You can prioritize penetration testing and red / purple teaming, attack and breach simulation on your high CIA systems and Internet accessible systems.
Security awareness training - No change
All your personnel should get this regardless of the systems they are touching
Supply chain security - CHANGE
You will want higher assurance levels of the controls at your suppliers if they are working on higher CIA systems, if for nothing else it provides a more defensible position in a legal battle when/if there is a security incident.
Threat modelling - No change
You want to threat model all your systems under change
Conclusion
Of the 27 standard cyber security controls I examined above only 4 (14%) change depending on the CIA rating. So maybe spend less time and effort on classification and more on implementing effective cyber security controls for all your systems.